Today is Data Privacy Day 2021! Privacy is celebrated each year on January 28th on Data Privacy Day creating a global community that respects privacy, safeguards data, and enables trust. 2020 may be remembered as the year of the pandemic; but it was also a year of significant developments in privacy risk management. We saw new frameworks adopted; Covid-19 data sharing apps; enforcement of CCPA and evolution with CPRA; stiff fines and enforcement actions for non-compliance; and invalidation of EU based data transfer mechanisms that impacted third party relationships. Rapid shifts to enable remote work have changed how organization secure and manage data in their environment.
An Evolving Privacy Landscape
Gartner predicts that the privacy landscape will continue to increase in complexity. By 2023, they predict that 65% of people across the world will have their personal information protected by modern global privacy regulations as compared to only 10% in 2020. The complexity of managing state by state and country by country privacy regulations continues to promote dialog for adoption of a Federal Privacy Regulation in the United States and consensus on privacy principles across international jurisdictions.
Managing readiness and compliance to shifting timelines for enforcement will keep data privacy front and center on company’s risk management “projects of the year” for the coming few years. It is not only new regulations changing the landscape – enforcement actions and interpretations have put many company’s compliance roadmaps into a tailspin. As outlined in a Q3 Shared Assessments blog, the decision to invalidate Privacy Shield puts a stronger focus on demonstrating adequate due diligence and updating contractual provisions between business partners. Even with the potential for a one-year transition period for addressing existing contracts with stronger standard contractual clauses, organizations still have work to do to maintain data maps, data inventories, and documentation on authorized data use across their third party inventories.
Data Privacy Governance Challenges in 2021
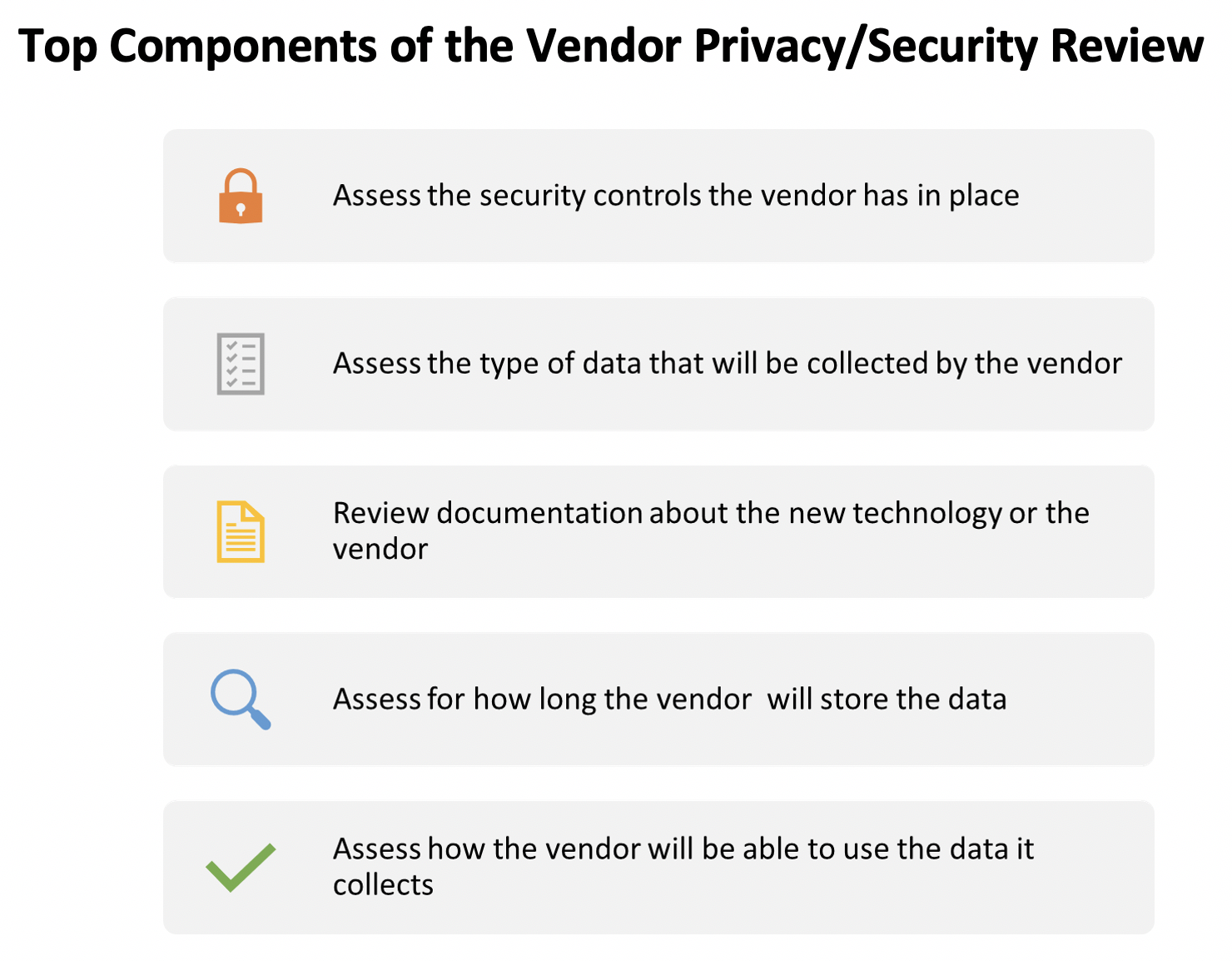
Data Governance is cited as one of the top data protection and privacy trends to watch out for in 2021, as reported in the Privacy Security Report in December 2020. Just like the pandemic put a spotlight on securing a remote workforce, the explosion of use of cloud technology and Internet of Things (IoT) puts a spotlight on transparency, ethics, and data governance. Modern digital ecosystems are based on an interconnected network of third party relationships. The International Association of Privacy Professionals (IAPP) and Ernst & Young (EY) published a Fall Report on Privacy in the Wake of Covid-19, a follow up to a survey done early in the pandemic. They found that during 2020 53% reported that privacy had increased in importance and 55% stated that safeguarding against cybersecurity risks had also grown in importance. Increasingly, another 40% said that meeting the expectations of clients and business partners had become a higher priority for their organization. The report outlined that roughly 33% to 38% were using expedited vendor privacy or security reviews in order to address immediate needs of the remote workforce.
IAPP/EY Privacy in the Wake of Covid-19 – Part Two Report
It is not sufficient to focus only on the information security controls, compliance today is about the privacy context of the data – throughout the data lifecycle. Data governance is a critical element of the due diligence process in third party relationships. While tools and workflow for GRC solutions have evolved, the actual collection and maintenance of vendor and data inventories has been challenging given a rapidly changing environment. The need to identify, assess, track, and update due diligence processes and contract terms between service providers and fourth party relationships will keep data privacy and compliance teams busy throughout 2021.
It all starts with the data – Using the Target Data Tracker
In response to these data governance challenges faced by industry sectors and members of the third party risk management community, the Shared Assessments program updated its’ core privacy tool for managing privacy risk in third party relationships, the Target Data Tracker (TDT). The Target Data Tracker (TDT) tool streamlines and simplifies the information-gathering process used in privacy reviews or assessments. The Target Data Tracker provides a due diligence tool to identify and track classifications and categories of data used by a third party, including the identification of locations and disclosures to fourth parties.
What is “Target Data?”
Target Data is an organization’s non-public information, protected health information, personally identifiable information, and similar data that is accessed, transmitted, processed, or retained by the organization or its independent service providers (fourth parties). Target Data can be defined by data owner/data subject and by specific regulatory jurisdictions or classifications of data. Each product/service/system that is provided by a third party requires a strong understanding of the data processing ecosystem.
The TDT focuses on six critical data governance areas to be addressed prior to beginning an evaluation of a service provider or as part of periodic third party risk assessments. Mature data governance requires the collection and maintenance of “data” about the “target data.” Such focus areas include:
- Who: Which entities collect, access, transmit, process, or retain personal data?
- What: What types of personal data are collected, accessed, transmitted, processed, or retained?
- Where: From what countries or locations does collection, access, transmission, processing, and storage/retention occur?
- When: When did collection, access, transmission, processing, or storage/retention start and end?
- Why: Why is the data used, or is the purpose of data usage authorized and defined in contracts?
- How: How and for what purpose is data shared with other Third or Fourth Parties?
Using the TDT in Third Party Risk Management
An Outsourcer can send the TDT to a third party service provider as part of the planning phase of a privacy assessment of the third party or as part of a privacy/security review. Likewise, a service provider can use the TDT as a compliance or due diligence artifact and proactively distribute it to clients in the third party risk assessment process. The tool can be utilized in multiple ways within the overall TPRM processes.
- Use the TDT to conduct a Pre-Assessment or for scoping vendors for data protection reviews
- Include the TDT in your Data Protection Impact Assessment (DPIA) process
- Include the TDT in your process to update and maintain vendor inventories
- Leverage the TDT as a due diligence artifact template or service provider record of processing
- Utilize the TDT to identify and track fourth party relationships
- Enable the tracking of service provider locations with current independent assurance reports
- Implement the TDT as part of your process for Acknowledgement/Certification or validation of service provider obligations for confidentiality, data use, retention, processing, and data safeguarding.
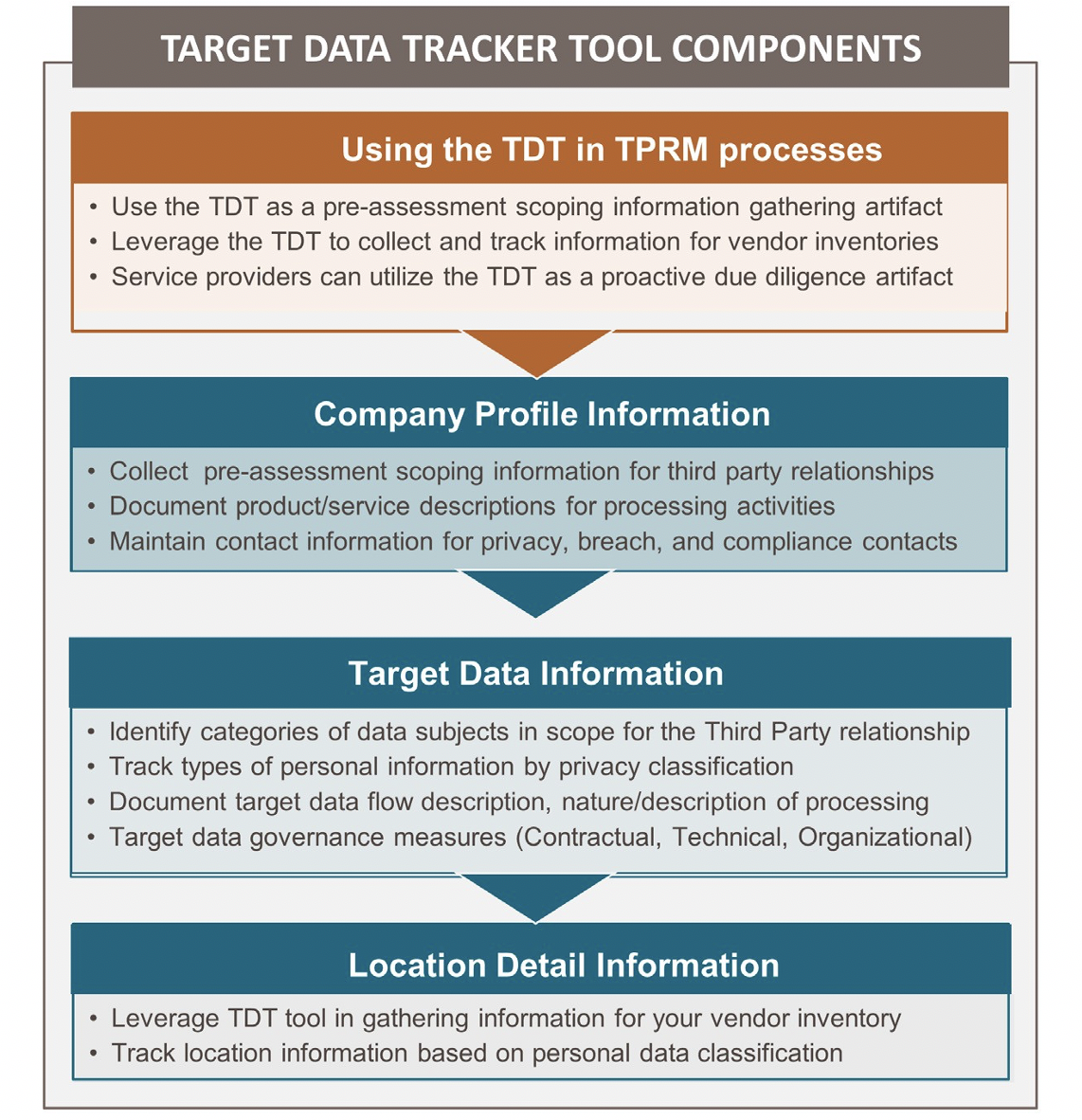
If You Collect it – Protect It is the starting point for good data governance for third party risk. Broadening the focus to the entire data processing ecosystem using the TDT can help organizations navigate conducting expedited privacy/security reviews or to create efficiency in the management of existing compliance software platforms to manage third party risk. International Data Privacy Day Champions aggregate and provide tools to support the principles of data protection. Here are several links to resources that can be used to enhance your third party risk management processes.
Download the Target Data Tracker Tool: https://sharedassessments.org/privacy-tools/
Additional Data Privacy Day 2021 Industry Resources:
- Manage Your Privacy Settings across Third Party Applications and Devices
- Review the Vendor Security Checklist to assess your current approach to third party risk


