We’ve been fielding many IoT (Internet of Things) questions this summer. Organizations who already use the SIG tool in their TPRM programs and organizations evaluating the SIG tool have asked us about the proper lines of inquiry around IoT. What questions do we need to be asking ourselves and our vendors to ensure IoT is secure? This blogpost offers IoT Risk Due Diligence Questions.
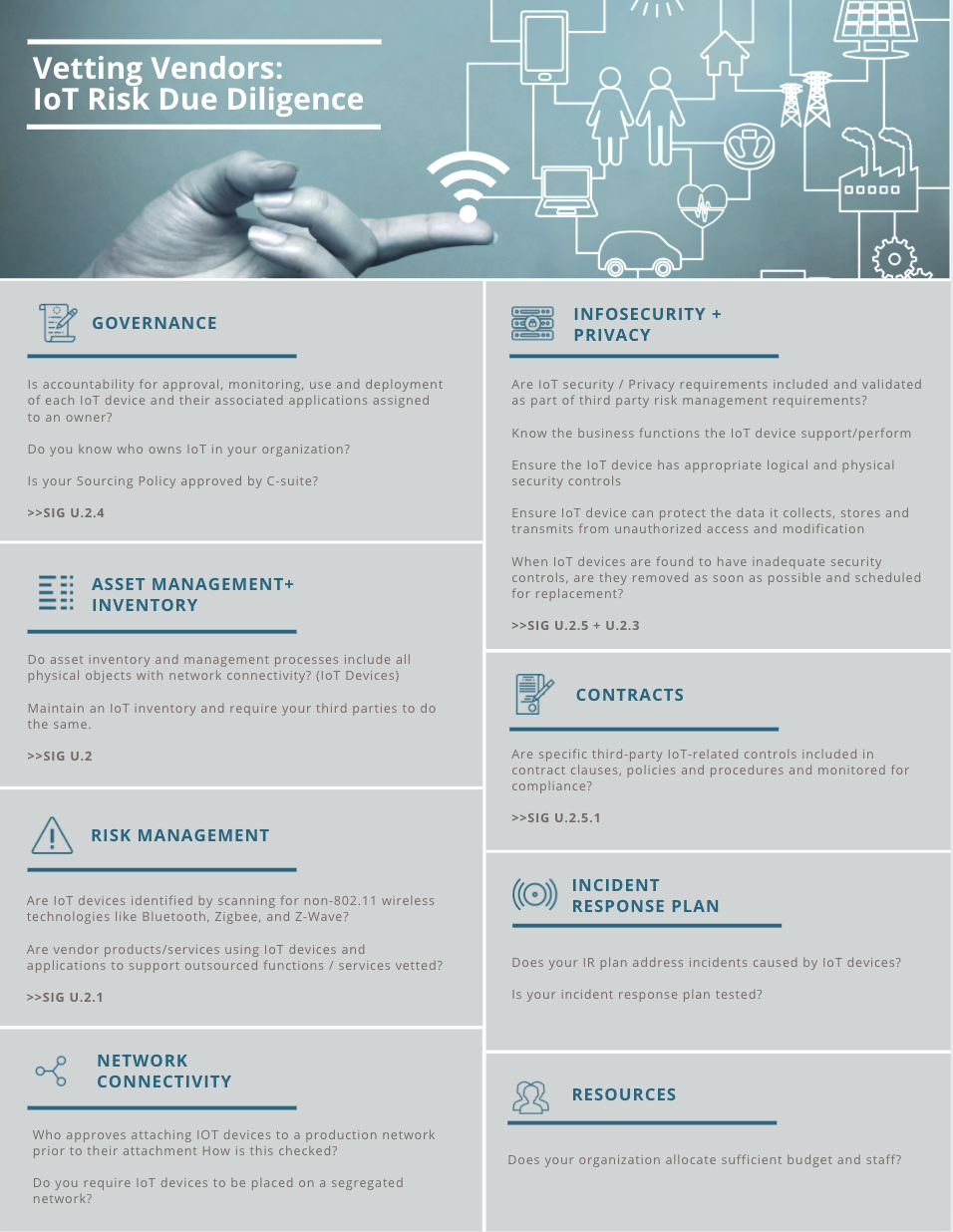
It has never been clearer that swift function improvements are needed throughout most IoT risk management and TPRM programs. The Standardized Information Gathering (SIG) Questionnaire Tool includes several questions (U.2…) for examining a vendor’s security hygiene specific to IoT. Also, we have created an IoT infographic (available as PDF here) with several questions pulled from our research report which may be useful as well.
These IoT risk related inquires come on the heels of A New Roadmap for Third Party IoT Risk Management – Shared Assessments’ collaborative study with the Ponemon Institute. The study underscores a major disconnect between senior leadership involvement regarding IoT related risk, that survey respondents say is essential from their Boards of Directors, and governance structures to address the expanding threat landscape. Clearly, the gap between understanding and practice must be closed, and quickly. It’s increasingly imperative that organizations get ahead of the problem and address IoT risks before a major disruptive event, not after one. This threat is NOW!
Recently, the FBI noted that it expects exploitation of mobile banking using a variety of techniques, including app-based banking trojans and fake banking apps. Increased use of Mobile Banking Apps Could Lead to Exploitation – Studies of US financial data indicate a 50 percent surge in mobile banking since the beginning of 2020. With city, state, and local governments urging or mandating social distancing, Americans have become more willing to use mobile banking as an alternative to physically visiting branch locations.
Similarly, Department of Homeland Security issued an alert affecting IoT medical devices. These IoT device and IoT application risks are likely to continue across all industries; increasingly impacting business disruptions to the delivery of products and services across the supply chain.
Feel free to use these IoT Risk Due Diligence Questions within your TPRM program.


