TPRM During the Pandemic: Emergent Responses To Emergent Times

Authors: Bob Jones, Tony Manley and John Bree
A changed world, a changed industry – this blogpost covers TPRM during the Pandemic.
The third party risk management community finds itself swimming in the maelstrom that has resulted from the shock to world systems generated by the pandemic. Having to work remotely (its own challenge), while concurrently having to identify and gauge the new risks presented by third parties’ remote working capabilities (particularly off-shore operators), is posing entirely new challenges to the risk community.
Every firm has its own IT/IS standards and policies that govern corporate hierarchy chain of command and operational challenges, such as BYOD use. The current situation requires a completely different mindset and analysis set. The due diligence rules of “what do I need to know and when do I need to know it” in order to ensure security in these unsecure settings has been radically altered.
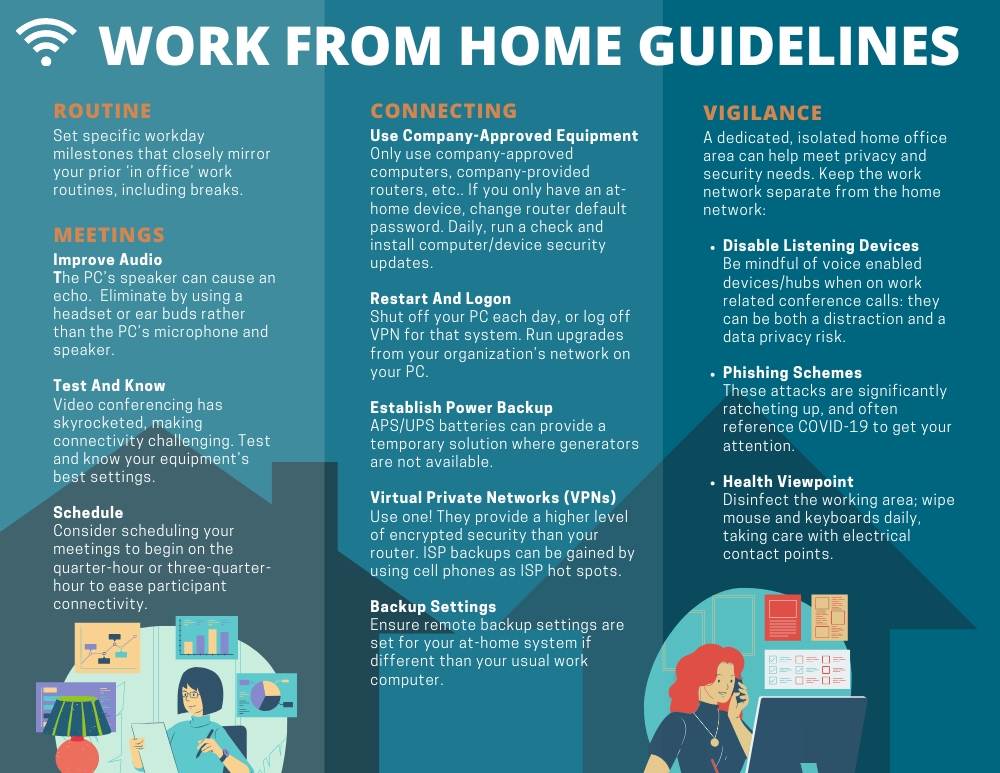
At its April 1st meeting, 26 members of the Shared Assessments Best Practices Awareness Group examined some of the best practices they have found to be useful around remote work hygiene. We hope others might find the following points covered by this blogpost and accompanying infographic of value in trying to rein in the risks associated with the vast majority of the workforce now operating in remote settings.
The Home Office – Best Practices:
For the work-at-home employee or contractor, a few guidelines are essential to help protect systems and information, as well as to maintain a higher quality and more productive work environment.
Establish a routine:
-
- Set specific workday milestones that closely mirror your prior ‘in office’ work routines, including breaks.
Upgrade and Maintain Systems:
-
- Connect only to company-approved equipment (computer, company-provided router, etc.). If you only have an at-home device, change the router default password.
- Daily, run a check and install computer/device security updates. Shut off your PC each day, or at least log off the VPN for that system. When you shut down and later logon, any upgrades from your organization’s network can be implemented on your PC.
- Establish a power backup where feasible. APS/UPS batteries can provide a temporary solution where generators are not available.
- Virtual Private Networks (VPNs) – Use one. They provide a higher level or encrypted security than your router.
- ISP backups can be gained by using cell phones as ISP hot spots.
- Make sure that remote backup settings are set for your at-home system if that is different than your usual work computer. Reach out to your IT department for help if you are unsure about how to accomplish this task.
Improve Meeting Experiences:
-
- Audio can be improved by using a headset or ear buds rather than the PC’s microphone/speaker. The PC’s speaker can cause an echo. Test and know your own equipment’s best settings.
- Video conferencing use has skyrocketed, making connectivity challenging. Consider scheduling your meetings to begin on the quarter-hour or three-quarter-hour to ease participant connectivity.
Maintain Vigilance:
-
- Be aware that individuals now in a shared at-home workspace may work for competitors. To the extent possible, avoid working in the same physical space (or within earshot).
- To the extent possible, having a dedicated, isolated home office area can help meet privacy and security needs. Absent that, keeping the work network separate from the home network should be attempted, as below.
- Disable listening devices when on work related conference calls. Be mindful of voice enabled devices/hubs – they can be both a distraction and a data privacy risk.
- Phishing schemes are significantly ratcheting up, and often reference COVID-19 to get your attention.
- From a health vigilance viewpoint – disinfect the working area; wipe mouse and keyboards daily, taking care with electrical contact points.
Of note, risk offshore can add layers of complexity to managing work at home environments. In particular, technology and security infrastructure is almost entirely lacking outside of established office buildings/complexes, the impact of which has not have been fully evaluated for operations and resilience. Office building/complex sites have backup generators, but homes and neighborhoods frequently do not. Of course, these issues can also affect the US, with rolling power black outs and bandwidth issues, especially in fire prone areas; and severe weather causing flooding and damage from tornados, hurricanes and winter storms.
Managing Third Party Risk in a Remote Environment – Where do we go from here?
From a risk manager’s viewpoint, focus primarily on compliance and controls, seeking higher levels of security that may be available without specific direction being provided to employees.
- Understand the capabilities/limitations of the residential internet infrastructure on a town/county/regional basis, including recurring weather patterns, power reliability, etc.
- Desktop as a Service – For those settings where the worker does not have access to a secure system, desktop as a service can potentially provide a significant gain in security hygiene. Bandwidth may need to be considered in factoring desktop as a service into your company’s plans.
- Be proactive in understanding and mitigating conflicts that can exist due to employees in a living arrangement with competitors’ employees.
- Adopting emerging endpoint device and IP integrity solutions can strengthen controls, including those for work at home employees.
- A shared responsibility model can be put in place across all users, so IT can better support users in their own setting.
Getting a handle on solutions and helping employees and contractors work at home more securely now will auger well for risk managers as future disruptive events inevitably occur.

